- Business
- Esoteric
- Fitness & Gym
- Health
- Hypnosis
- Management
- Marketing & Selling
- Massage – SPA
- Parenting
- PUA Seduction
- Science
- Self Improvement
- Art
- Investing
- Painting & Skulping
- Tai Chi & Martial Arts
- Qigong
- Taoism
- Design & Graphics
- Medicine
- Exams
- Spirituality & Religion
- Hobbies & Fixing & Woodworking
- Photography & Film Making
- Networking & Lan
- Forex & Trading
- IQ & Memory
- Vision & Eye Care
- Swimming & Scuba diving & Water Sports
- Security & Hacking
- Travel
- Cooking
- Driving & Flighting
- Languages
- Computers & Programming
- Building & Home Improvement
- Music
- Astronomy
- History
- Mathematics
- Philosophy
- Literature & Writing
- Economics & Finance
- Sewing
- Hunting
- Electronics
- Psychology & Psychiatry
“Hacking Buffer Overflow Made Easy” has been added to your cart. View cart

Crack Job Interviews with AI: Ace Interviews with Confidence
$20.00 Original price was: $20.00.$5.00Current price is: $5.00.
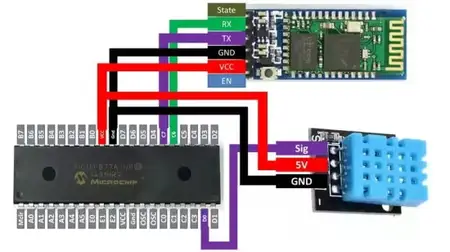
DH11-DHT22 Temp and humidity sensor interface PIC16F877A MCU
$20.00 Original price was: $20.00.$5.00Current price is: $5.00.
Cybersecurity Introduction by Jason Rowsell
$20.00 Original price was: $20.00.$5.00Current price is: $5.00.
Category: Security & Hacking
Description
Published 4/2025
MP4 | Video: h264, 1280×720 | Audio: AAC, 44.1 KHz, 2 Ch
Language: English | Duration: 1h 33m | Size: 589 MB
Understand the fundamentals of cybersecurity and its importance.
What you’ll learn
Understand the fundamentals of cybersecurity and its importance.
Identify and assess common cyber threats and vulnerabilities.
Understand essential concepts of encryption, authentication, and access control.
Understand the basic security controls to protect systems and data.
Explain key types of Malware and their differences.
Learn about common Cyber Security tools and standards organizations.
Requirements
No prior cybersecurity knowledge required.
Basic understanding of computers, operating systems, and networking concepts.
An interest in learning the main concepts of Cybersecurity, and how they fit together.
Description
In today’s hyper-connected digital world, cyber threats are not just common – they are constantly evolving and becoming more sophisticated. Whether you’re an aspiring cybersecurity professional eager to break into the industry, an IT professional looking to expand your skill set, a small business owner aiming to safeguard your systems and sensitive data, or simply someone who wants to protect your personal information from online threats, understanding the fundamentals of cybersecurity is no longer optional – it’s essential.What You’ll LearnBy the end of the course, you will:Grasp core cybersecurity principles and terminology.Recognize and respond to phishing, malware, and social engineering attacks.Secure systems through encryption, access control, and authentication methods.Implement basic security measures to protect networks and applications.Understand compliance frameworks (NIST, ISO 27001, PCI-DSS) and how to align security policies with regulatory standards.This course equips you with foundational knowledge and practical skills to:Identify and mitigate common cyber threats.Apply essential security practices to protect systems and data.Understand encryption, authentication, and access control concepts.Recognize phishing, social engineering tactics, and respond effectively.Navigate compliance standards and risk management frameworks.Why Take This Course?Practical Insights: Real-world examples and case studies.Comprehensive Content: Covers a wide range of cybersecurity fundamentals.Career Advancement: Ideal for IT pros looking to transition into cybersecurity roles.Protect your digital assets and build a strong cybersecurity foundation – enroll today!
Who this course is for
Anyone seeking a good high-level introduction to key Cybersecurity concepts.
Students
Business Owners
IT professionals transitioning into security roles
Beginners interested in cybersecurity
Homepage
https://www.udemy.com/course/cybersecurity-introduction/
Shipping & Delivery
DIGITAL DELIVERY ONLY
This is digital product THE DOWNLOAD LINK SEND 12-24 HOURS AFTER UPON PURSUASE AND PAYMENT CLEARS"
- The digital files are uploaded on PCLOUD
- 12-24 hours delivery time
- the download links expire after 7 days and need to download them
- to renew the download link after expiration have one additional fee $5 per product
REQUESTS
Also we accept requests (in this page) and course exchanges
In Course exchanges we are sending credits only
The credits will be the same price as we can sell course
"REFUNDS & RETURNS"
No Refunds on digital product
ONLY EXCHANGE
- Because of the abuse of the refunds from many customers i don't accept refunds
- We accept only 1 time exchange with product of the same price
- if you done mistake on the exchangeable product i don't recognize it as your mistake
- Exchanges only 3 days after the payment of your digital product. (if abused again i will do it 1 day)
Related products
Cyber Security – Go From Zero to Hero (2020)
Ultimate Ethical Hacking Course – Learn From Scratch
$5.00
Windows Performance Toolkit: Virus Analysis
$5.00
Practice Your First Penetration Test: Kali & Metasploit Lab
$5.00
Getting Started with Reverse Engineering
$5.00
Nmap Network Security Scanning Basics & Advanced Techniques
$5.00
The Complete Hacking Course – Go from Beginner to Advanced
$5.00